Built to solve one core problem:
Process Pll Data in encrypted form, without decryption.
Secure-by-Design Architecture
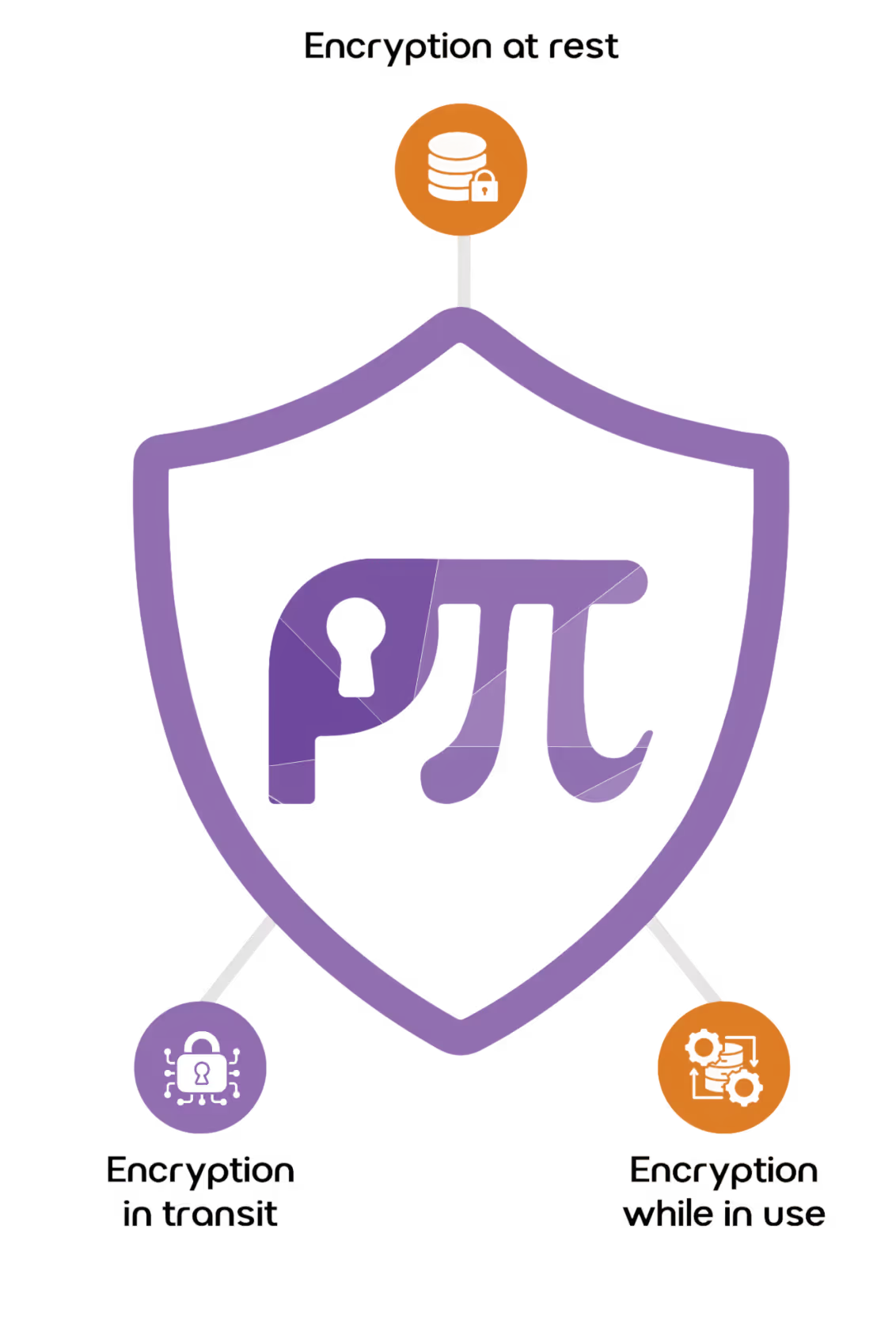
How PII Data Vault Protects Data While It's Being Used
Traditional encryption is excellent for data at rest or in motion, but it fails when data is in use. To search or analyze data, organizations have to decrypt PII, creating windows of vulnerability. PIl Data Vault utilizes Searchable Encryption and Cryptographic Computing to close this window.
Business operations require searching customer data using combination of names, IDs. dates, or identifiers.
PIl Data Vault uses searchable encryption, which allows the system to:
- Perform exact and fuzzy searches
- Match customer identities
- Validate records
All without decrypting the underlying data. Applications receive only secure tokens or encrypted results. not plain text.
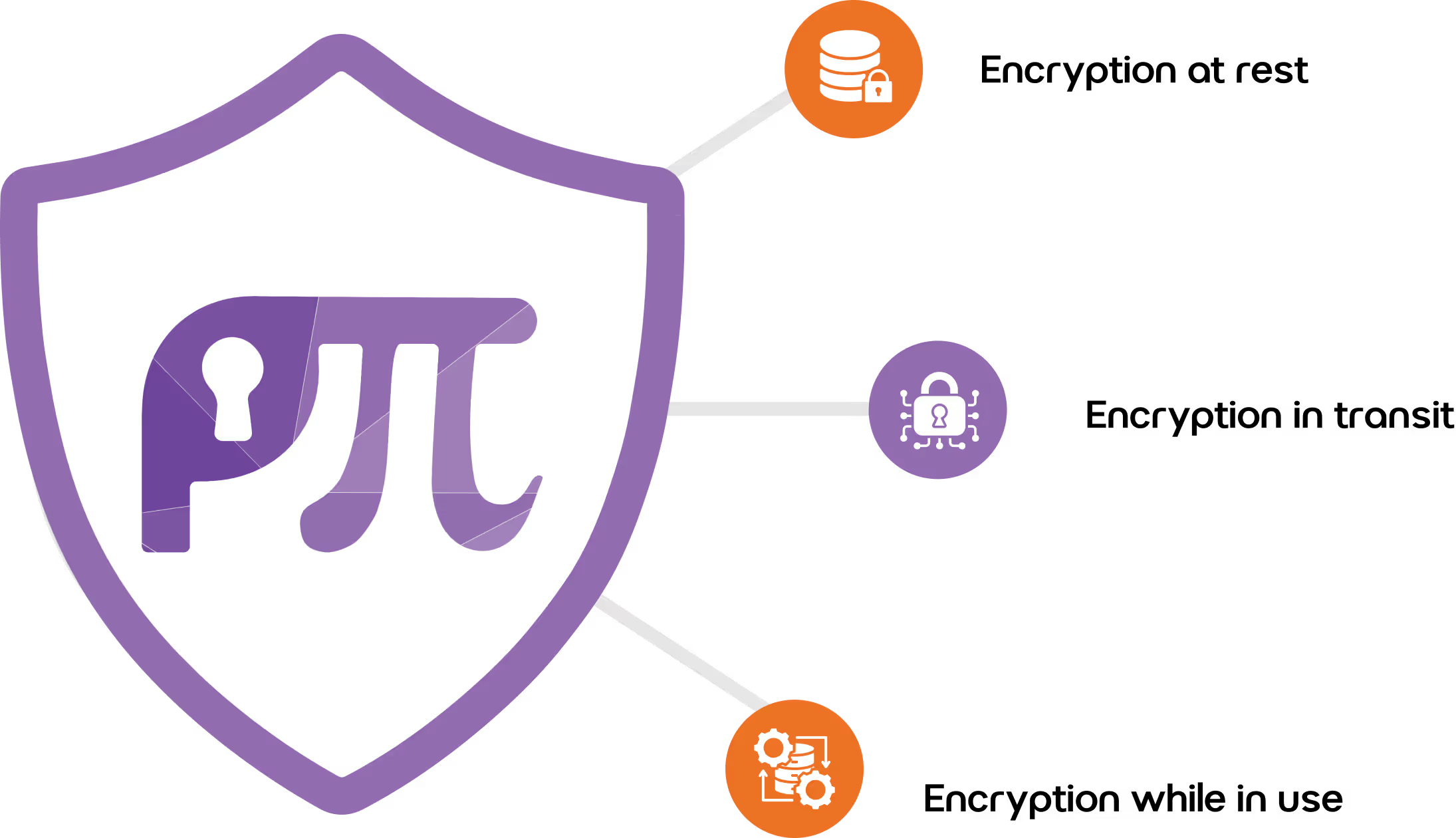
Searchable Encryption Technologies
Unlike standard encryption, Hashcryption cannot be reversed to find the original value
NIST-approved algorithm maintains the original data format so a 10-digit phone number remains a 10-digit token
Enables mathematical operations on encrypted values of all data elements (strings, dates, numbers)
PII Data Vault is Quantum-Safe
PIl Data Vault uses following components: Post-quantum cryptographic principles and cryptographically certified components
SHA 3-512
AES 256/512, X CHA CHA 20
FHE, FPE (FF-1, FF3-1), ZKP, Posidex Hashcryption with AES 256
ML- KEM, Kyber
FIPS 140 - 3

.svg)